A better way to conduct security assessments?
The vendor security assessment process is too long, inefficient and time consuming. A much better way to perform vendor security assessments would be to use the body of unbiased content that already exists in most companies: the security policy. Here we show you how.

The traditional approach to security assessments
In 2020, the global average cost of a data breach was $3.86 million, according to Ponemon’s Cost of a Data Breach Report. The report also notes that should a third party cause the data breach, the cost will increase — by more than $370,000. It is no wonder that in the wake of GDPR and large data breaches, organisations require due diligence from their third party vendors, usually in the form of security questionnaires.
A security questionnaire assesses your, a vendor or third party’s technology systems, physical security and policies. As illustrated in Figure 1, an overarching security assessment plan will often involve the following entities: assessment, review, identify risks, remediation and risk register:
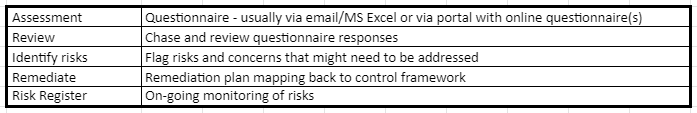
Figure 1: Vendor security assessment process
The traditional approach to security questionnaires is manual and inefficient. Organisations send out the security questionnaires in the form of spreadsheets or documents. Often supporting documents must also be submitted as evidence. Responding to security questionnaires takes time, energy and resources. Frequently, security questionnaire content is stored on systems like Google Drive, Sharepoint or other databases. The security questionnaire response process may be managed via Excel or a project management tool. Respondents will have to search through a number of individual documents to find answers, having to manually extract the content repeatedly. Sifting through the documentation to understand risk posture and setting up remediation plans is a gargantuan task – imagine the auditing process for a thousand or more vendors…
On the other hand, an automated platform provides a collaborative environment where questions can be clarified, evidence viewed and remediation discussed. Is it time to move beyond the traditional and towards a more forward-thinking approach?
Rethinking the annual questionnaire
Information security risks assessment is the first step towards finding and correcting vulnerabilities that could lead to an information breach. It is a crucial tool in creating a cost-benefit analysis for selecting appropriate controls based on risk and business needs. Using an automated information security risk assessment tool will:
- simplify data collection
- aid in identifying current risks
- evaluate risk severity
- predict possible future events
- automate follow-ups
- enable standardisation
Automating the risk assessment process will also be greatly sped up. Whereas manual assessment requires 4 weeks per entity to be conducted, automation reduces this down to only one hour (Figure 2, below). Also illustrated is the significant cost and resource reduction automation provides over the traditional, manual process.
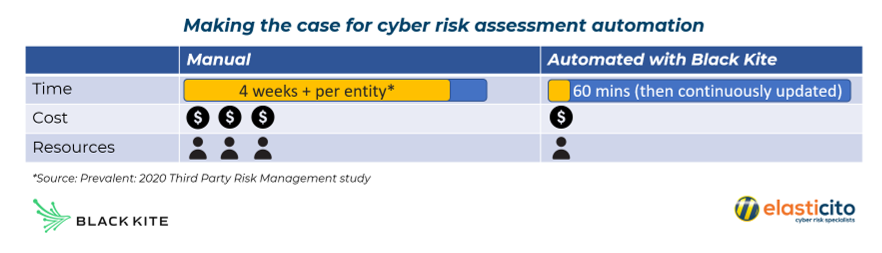
Figure 2: Time, cost and resource comparison of manual vs automated cyber risk assessment
Most organisations have security policy documents that they maintain for audit and other purposes. An organisation’s cyber security policy outlines the guidelines for transferring company data, accessing private systems and the use of company issued devices. These documents generally reflect a true and realistic view of the state of security policies, controls and processes internally. It is these documents that are used to automatically answer vendor security questionnaires using Black Kite’s patent pending Universal Parsing Engine. “With Black Kite, you can transform a week’s work into one hour”, says Elasticito CEO Ronan Lavelle.
Figure 3 clearly illustrates the opportunities to automate the VCRM lifecycle. With an effective and reliable automated security system, your organisation’s manual effort will be reduced and the speed of internal processes increased. Using Black Kite’s Strategy Report, you can easily share questionnaires with vendors. Vendors can complete the questions and the answers can then be mapped to regulations and frameworks in the system.
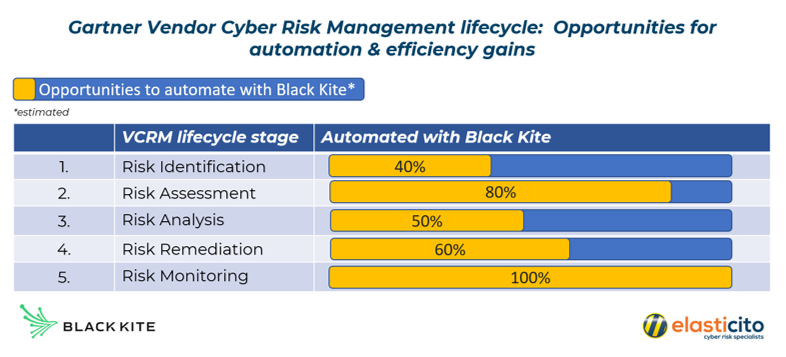
Figure 3: Opportunities for automation in the VCRM lifecycle stages.
Cyber security risk assessments have long been a function of IT security professionals. Increased awareness and a growing need for industry-wide compliance have driven the importance of cyber risk assessment automation as an integrated and integral part of an overall information security program. CISO’s can use tools such as Black Kite to gain greater visibility into the risk posture of their organization, determine how threats and vulnerabilities may be impacting business operations, and determine how best to mitigate those risks to meet compliance and regulatory requirements.
Black Kite’s rating technology uses OSINT to compare vendor cybersecurity to industry standards. As illustrated in Figure 4, below, Black Kite assigns a probable financial impact rating to your organisation’s risk posture using OpenFair.
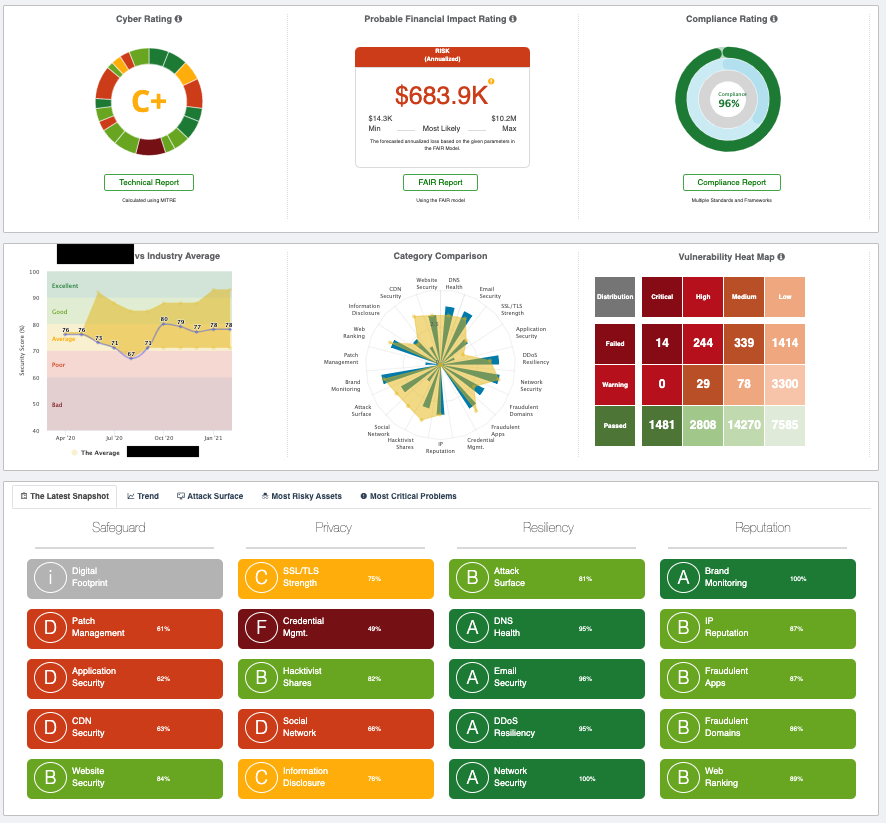
Figure 4: Black Kite dashboard
An automated security assessment solution will increase the efficiency of conducting third-party risk assessments, which can reduce the time to remediation, as well as the amount of time that exploitable vulnerabilities go unaddressed in an environment.
The key to implementing successful automation technology is choosing a product that integrates with your organisation’s existing processes and can effectively manage your third parties and vendors. Contact the Elasticito team for more information.
